In February 2026, a critical security flaw was identified on Ledger wallets connected to certain Android smartphones. According to Google Play Services data, approximately 25% of Android devices in circulation are affected by this vulnerability. For an investor holding even €50,000 in crypto assets, this information warrants immediate attention. The question of maintaining a secure crypto wallet on Android smartphones has become paramount.
What makes this situation particularly tricky: the vulnerability doesn't affect the hardware wallet itself, but rather the interface between the Ledger Live mobile app and certain Android versions. A malicious actor with physical or remote access to your smartphone could potentially intercept sensitive information during your transactions.
This flaw raises a fundamental wealth management question: can you still safely use your Android smartphone to manage your crypto assets? The answer is yes, provided you understand the risks precisely and apply the best practices I detail below.
Anatomy of the Ledger vulnerability: what's actually at risk
Contrary to the alarmist headlines that circulated, this flaw does not expose your private keys. The fundamental principle of hardware wallets remains intact: your keys never leave the Ledger device itself. What is potentially compromised is the communication between your smartphone and your Ledger during a transaction.
Concretely, an attacker exploiting this ledger vulnerability crypto could theoretically modify the destination address of a transaction during validation. Imagine you want to send €10,000 in USDC to your Kraken account. Without you noticing, the address displayed on your smartphone could be swapped for that of an attacker, even as you confirm the transaction on your Ledger.
There is a safeguard: it relies on systematically verifying the destination address on the Ledger screen itself, not on the smartphone. This is precisely why hardware wallets have a physical screen. But let's be honest: how many users actually verify, character by character, a 42-character alphanumeric address before confirming?
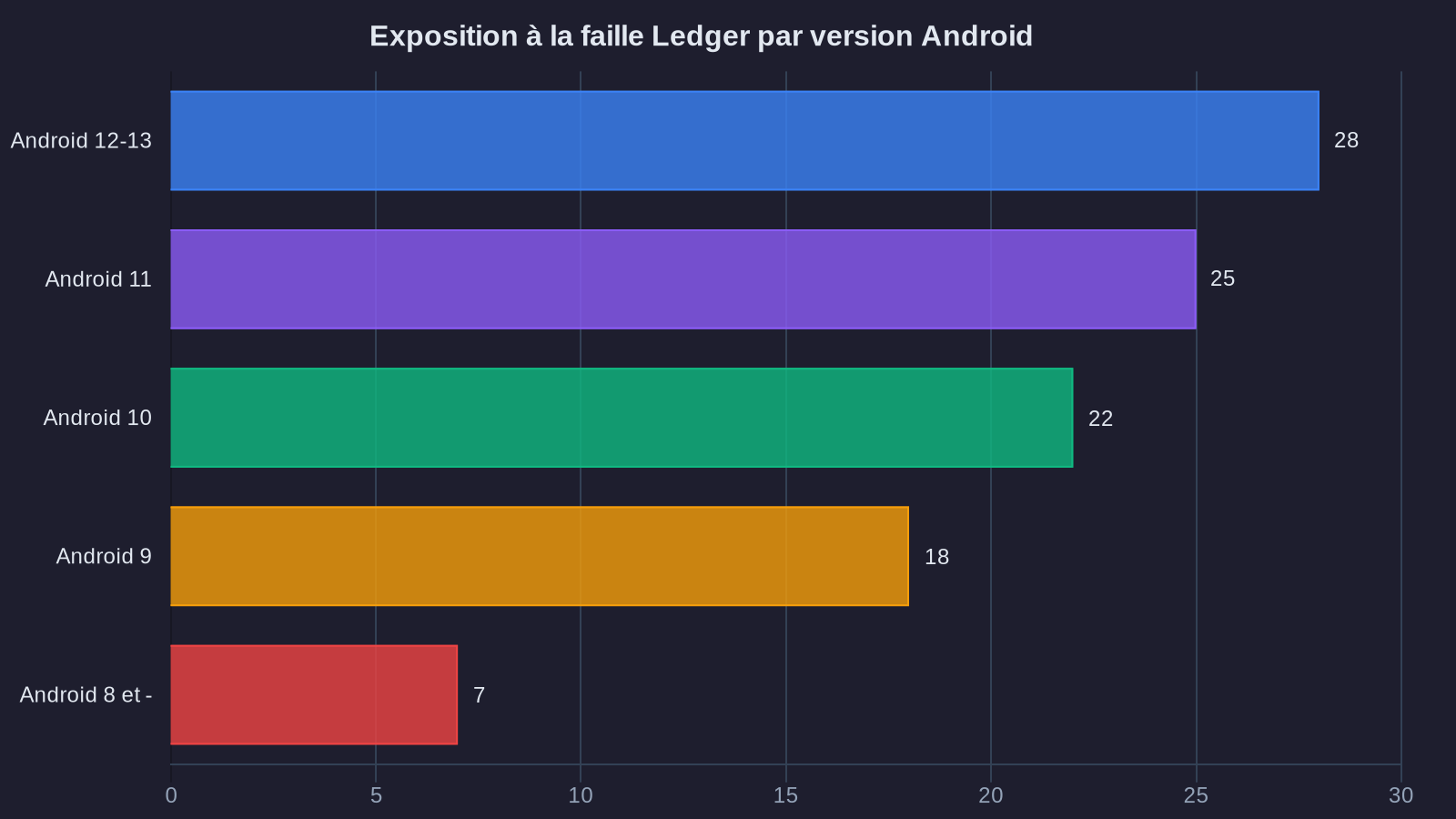
The affected Android versions are primarily those before Android 12, which still represent 28% of installed devices according to February 2026 statistics. If your smartphone is more than three years old and hasn't received the latest security updates, you're potentially in the risk zone.
Wealth assessment: when risk becomes unacceptable
Let's frame this from a wealth perspective. If you hold €100,000 in crypto assets, what level of risk exposure are you willing to accept for the convenience of using your smartphone daily?
Compare this with traditional finance. Your private bank would never allow you to make a €50,000 transfer without at minimum two-factor authentication and confirmation through a separate channel (SMS, phone call). In the crypto world, we should apply the same level of rigor.
Here's my analysis framework based on the amount held:
Crypto assets under €10,000: An up-to-date Android smartphone (version 12 minimum) with Ledger Live remains an acceptable solution. Risk exists but remains proportionate to the amount. Systematically verify addresses on the Ledger screen, particularly for transactions exceeding €1,000.
Crypto assets between €10,000 and €50,000: An intermediate zone. I recommend segmentation: use your Android smartphone for routine transactions (dollar-cost averaging, small arbitrage), but switch to a dedicated computer for significant movements. An old Linux laptop, used solely for your crypto operations, represents a €300 investment that's easily justified.
Crypto assets exceeding €50,000: At this level, using a smartphone as your primary management tool becomes difficult to justify from a wealth perspective. The optimal setup consists of a dedicated computer, ideally running Linux, used exclusively for your crypto operations. Some of my clients even use two Ledgers: a "hot" one for routine operations (5-10% of assets), and a "cold" one never connected to the Internet except for significant movements. This approach echoes the principles discussed in our analysis on generating passive yield on crypto assets, where capital security takes priority over immediate accessibility.
Security protocol: concrete measures to protect your mobile wallet
Beyond theoretical analysis, here are the actions I recommend implementing within 48 hours if you're currently using an Android smartphone to manage your crypto assets. These android crypto protection measures are essential.
First step: audit your current setup. Check your smartphone's Android version (Settings > About Phone). If you're running Android 11 or earlier, you're in the risk zone. Also check the date of your last security update. If it's more than three months old, your device isn't being properly maintained.
Second step: update your ecosystem. Update Android to the latest version available for your model. Update Ledger Live to version 2.73 minimum (available since March 2026), which includes additional protections against this vulnerability. Update your Ledger's firmware itself.
Third step: create a whitelist of addresses. For your frequent destinations (exchanges, other personal wallets), create a list of verified contacts in Ledger Live. Take the time to verify each address once, manually. After that, only send funds to these pre-validated addresses. This simple measure eliminates 90% of the risk.
Fourth step: systematic verification protocol. Before any transaction exceeding €500, I recommend this three-step process: first, verify the address on your smartphone. Next, verify it on the Ledger screen, comparing at minimum the first six and last six characters. Finally, for significant amounts (more than €5,000), make a test transaction of €10 to the new address first, wait for confirmation, then execute the main transfer.
These measures may seem cumbersome. They are. But think of them as equivalent to a safe for your important property documents. Nobody finds it excessive to physically protect property titles or life insurance contracts. Your crypto assets deserve the same level of protection.
Beyond the smartphone: rethinking your mobile wallet security strategy
This Ledger flaw on Android reminds us of a reality often overlooked: securing a digital portfolio doesn't end with buying a hardware wallet. It's a chain only as strong as its weakest link.
I regularly observe this paradox among investors: they buy a €150 Ledger to secure €80,000 in crypto assets, then use it with a four-year-old Android smartphone that hasn't been updated in two years and connects to public WiFi at their favorite café. It's like installing a reinforced door on a house while leaving the windows open.
The question isn't whether smartphones are inherently dangerous for managing crypto assets. The real question is: what security architecture matches the level of wealth you're managing? An investor holding €200,000 in crypto should apply the same security standards as a company protecting its digital assets. Besides, if you're considering significant long-term positions, our analysis on Bitcoin at $1 million shows why security becomes crucial given valuation projections.
This potentially means reconsidering your setup: a dedicated computer (€300-500), a hardened operating system (Linux Tails or Qubes OS, free), a second Ledger for cold storage (€150), and ideally a multisignature system for your largest holdings. On a €150,000 portfolio, this €1,000 investment in security infrastructure represents 0.66% of the total. That's negligible compared to the cost of a security breach.
This approach may seem maximal. It is, admittedly. But after fifteen years observing crypto market dynamics, I've found that security-related losses almost always happen to investors who made "reasonable" compromises. In wealth security, maximalism isn't paranoia—it's elementary prudence.
What this means for your portfolio
The Ledger vulnerability on Android doesn't mean you should abandon your smartphone as a crypto management tool. It means you should calibrate your security setup to match the amount you're managing.
For a portfolio under €10,000, a recent, up-to-date smartphone used rigorously (systematic address verification, contact whitelist, test transactions) remains an acceptable solution. Beyond that, and particularly above €50,000, the question deserves to be reframed: why take a risk, however minimal, when alternative solutions (dedicated computer, dual hardware authentication) represent only a tiny fraction of the portfolio you're protecting?
Securing your crypto assets isn't a cost. It's a wealth investment just like your home insurance or bank safe deposit box. In an environment where attacks are becoming increasingly sophisticated, the real question is no longer "how can I safely use my smartphone," but rather "what custody architecture matches the level of wealth I'm managing."
Your wealth deserves more than a savings account. I'll show you the way, with numbers to back it up.
```


