In December 2024, Vercel confirmed a security breach that exposed authentication tokens. For crypto developers, the diagnosis hit hard: potentially compromised API keys, vulnerable deployment wallets, and a race against time to limit the damage.
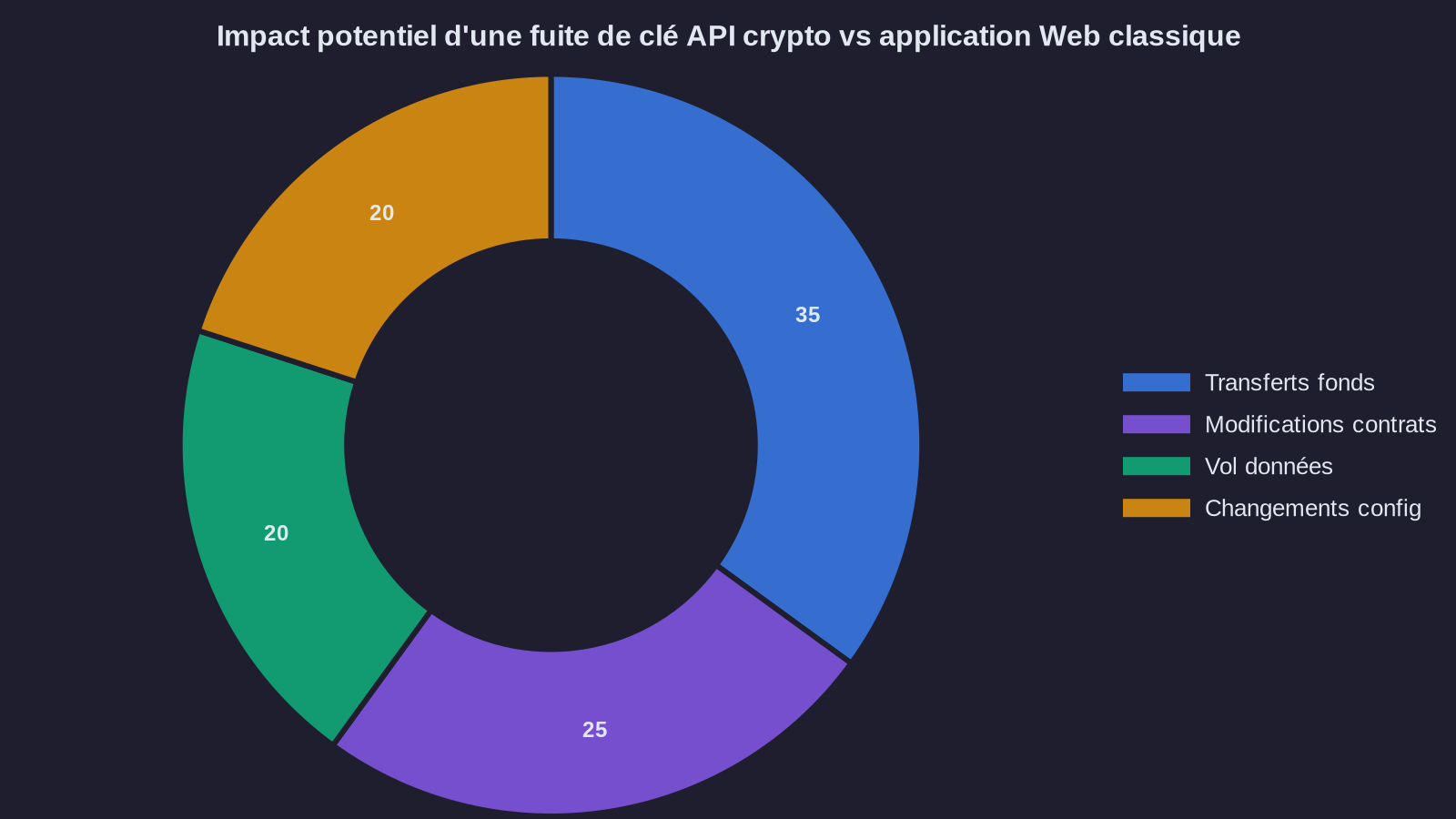
This type of incident isn't new in the blockchain ecosystem. But the Vercel leak reveals a reality often underestimated in supply chain security: in a crypto project, a single exposed API key can open the door to fund transfers, smart contract modifications, or theft of sensitive data. Unlike a standard web application where a token leak only allows content modification, here the impact is immediate and financial.
If you've deployed crypto applications on Vercel, or if you use similar services (Netlify, Railway, Render), here's what you need to do right now. Not tomorrow. Now.
The first 3 hours: revoke your API keys before investigating
The classic mistake when suspecting a leak? Wanting to understand the scope of the problem first before taking action. That's the worst incident response strategy. While you're auditing your logs, an attacker could already be draining a deployment wallet or modifying critical configuration.
First action: revoke all sensitive crypto API keys. We're talking about developer credentials that enable financial operations or smart contract modifications. Concretely:
- Exchange API keys (Binance, Coinbase, Kraken): immediate revocation through the exchange dashboard
- Node provider keys (Infura, Alchemy, QuickNode): generate new keys with rotation
- Crypto payment service keys (Stripe Crypto, Coinbase Commerce): deactivate then regenerate
- Private keys of deployment wallets: transfer funds to new addresses generated on a secure device
This first phase takes between 30 minutes and 2 hours depending on your infrastructure complexity. It's a mandatory investment. A compromised exchange API key can enable fund withdrawals in minutes if withdrawal limits allow it.
Second action: isolate production environments. If you're using Vercel environment variables to store secrets, assume they've been exposed. Immediately create a new clean production environment with new keys and switch traffic to it. The old environment stays read-only during the audit.
Post-incident audit: reconstructing the exposure timeline
Once access is revoked, you can investigate safely. Your incident response goal: identify what was accessed, modified, or stolen. For a crypto project, three areas require priority auditing.
Area 1: API logs from external services. Most exchanges and node providers keep a history of API calls. You need to check:
- Requests from unusual IP addresses (note that Vercel uses dynamic IPs, but an attacker typically goes through an identifiable VPS or proxy)
- Sensitive actions: withdrawal order creation, limit modifications, balance queries
- Suspicious timestamps: activity outside your normal deployment hours
Real example from a DeFi project in 2023: after an Infura key leak, the team detected 47 eth_sendRawTransaction calls from a Ukrainian IP, even though no deployment was planned. The transactions didn't go through (the deployment wallet was empty), but the intent was clear. A situation that echoes the systemic vulnerabilities exposed in the Resolv hack.
Area 2: Vercel deployments. Vercel maintains a history of all deployments. Check if any unauthorized deployments were triggered during the compromise period. An attacker could have injected malicious code in a build, for example to exfiltrate user data or redirect transactions.
Compare deployed code with your Git repository. If you detect a difference, consider that deployment compromised and immediately revert to a clean version.
Area 3: on-chain transactions. If you use deployment wallets to interact with smart contracts, audit all transactions emitted by these addresses. Use a blockchain explorer (Etherscan, BscScan, etc.) and check:
- Unrecognized transactions (transfers, token approvals, function calls)
- Unlimited approvals (
approve(spender, type(uint256).max)) that could be exploited later - Interactions with unknown contracts
This audit phase typically takes 4 to 8 hours for a medium-sized application. On a complex project with multiple wallets and dozens of APIs, expect a full day.
API key management: rethinking secret storage
Once the crisis is handled, you need to understand why you were vulnerable. The reality is that storing crypto API keys in Vercel environment variables (or equivalent) is a poor practice for supply chain security. It's convenient, it's fast, but it's risky.
Crypto developers must adopt a differentiated approach based on key sensitivity. Here are three security levels for effective API key management:
Level 1: read-only keys. Keys that only allow data queries (balances, transaction history) can stay in standard environment variables. The risk is limited to information leakage, not financial loss. Example: Etherscan API key to display a wallet balance.
Level 2: keys with limited permissions. For keys that enable sensitive but controlled actions (withdrawal orders with limits, calls to non-financial smart contracts), use a dedicated secrets manager like AWS Secrets Manager, Google Secret Manager, or HashiCorp Vault. These services provide:
- Encryption at rest and in transit
- Granular access control (IAM)
- Complete audit trail of secret access
- Automatic key rotation
Average cost: between $0.40 and $1 per secret per month depending on access volume. That's negligible compared to the risk.
Level 3: critical keys (private keys, signing keys). These developer credentials should never be stored in a third-party service, even encrypted. Two options:
- Hardware Security Module (HSM): professional solution for high-stakes financial projects. An HSM like AWS CloudHSM or a Ledger Nano for manual deployments ensures the private key never leaves the secure device. Cost: starting at $1,500 per month for cloud HSM.
- Multi-signature with threshold (threshold signature): instead of a single key, use a 2-of-3 or 3-of-5 scheme. Even if one key is compromised, the attacker can't do anything alone. Solutions like Fireblocks, Qredo, or Gnosis Safe enable managing this type of architecture.
Example of a secure architecture for a DeFi protocol:
- Vercel environment variables: only read keys (Etherscan API, The Graph API)
- AWS Secrets Manager: Infura/Alchemy keys with blockchain read permissions
- Gnosis Safe 3-of-5: smart contract deployment wallet, with 3 keys held by different team members, 2 keys in cold storage
This architecture makes a Vercel compromise nearly risk-free: an attacker only gets read-only keys, useless for stealing funds or modifying contracts. An approach that shares certain principles with DeFi protocol protection mechanisms.
The supply chain security watchpoint
An incident like the Vercel leak reveals a fundamental tension in crypto development: deployment speed (automated CI/CD, accessible environment variables) versus security (HSM, multi-signature, manual validation). Many teams optimize for velocity during launch, then realize too late that their deployment infrastructure has become a single point of failure.
The lesson: in a crypto project, a compromised private key isn't a security incident, it's direct financial loss. There's no rollback possible on a public blockchain. There's no customer service to cancel a transaction. Once funds are gone, they're gone.
If you're developing on crypto, assume your deployment platform (Vercel, Netlify, or otherwise) will be compromised someday. That's not pessimism, it's realism. The real question isn't "if," but "when." And when it happens, your architecture must guarantee that the attacker can't do anything with the secrets they obtain.
Final point: notify your users if a breach is confirmed. GDPR Article 4 requires notifying the data protection authority within 72 hours in case of personal data breach. If your incident exposed wallet addresses, emails, or transaction data, that's the case. Transparency is a legal obligation, but it's also a matter of trust. Crypto projects that downplay or hide security incidents always end up losing their community.

