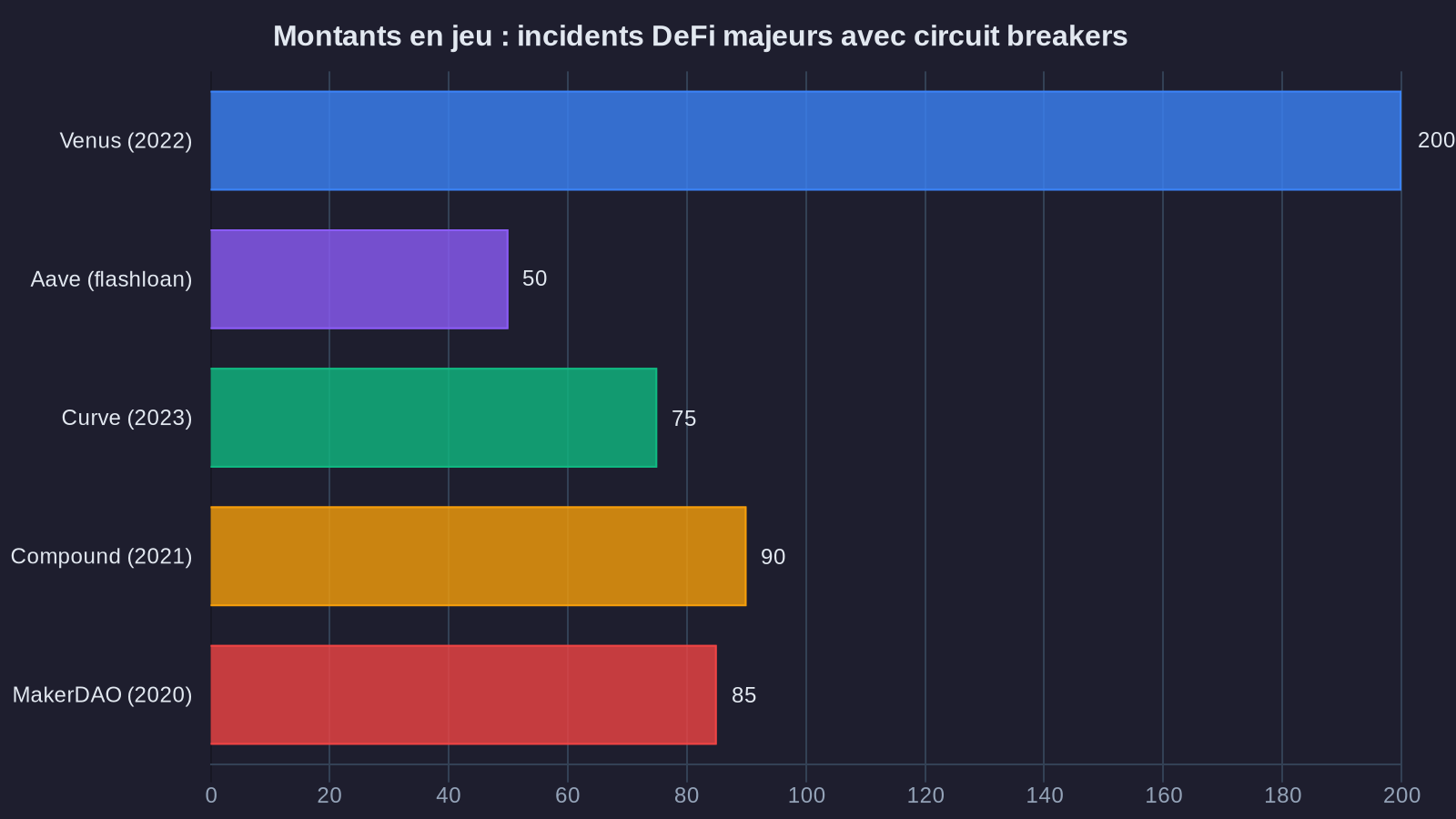
In September 2022, the Venus protocol on BNB Chain came dangerously close to disaster. An attacker attempted to manipulate the XVS token price by injecting massive amounts of funds, hoping to trigger a cascade of liquidations that would have emptied the protocol's reserves. The stakes? Over $200 million. Yet the attack failed.
What saved Venus was a mechanism few users understand: a circuit breaker. Think of it like an electrical fuse in your house. When voltage becomes dangerous, it automatically cuts the power to prevent a fire. DeFi protocols have developed the digital equivalent to protect user funds against real-time exploits.
But how does this protection actually work? And more importantly, is it really effective when millions evaporate in seconds?
The fundamental problem: attack speed
In traditional finance, if something goes wrong, you can call your bank. A human can block a suspicious transaction, freeze an account, launch an investigation. The banking system operates with business hours, processing delays, and multiple validation steps.
DeFi is the complete opposite. Smart contracts execute code 24 hours a day, 7 days a week, non-stop. Once a transaction is validated, it's final. There's no way to reverse it. And crucially, an attacker can chain dozens of operations in seconds—the time it takes for a block to be validated on the blockchain.
Let's look at a concrete example. In 2021, the Cream Finance protocol suffered a flash loan attack. The attacker instantly borrowed $500 million without collateral, manipulated the prices of multiple tokens, then repaid the loan while pocketing $130 million in profit. All in a single transaction, validated in 13 seconds.
Facing this reality, development teams understood they needed to automate defense at the same level as the attack: in real time, directly in the code. This approach fits into a broader strategy of securing crypto assets that concerns both protocols and individual wallets.
DeFi circuit breakers: fuses programmed into code
A circuit breaker is like an automatic safeguard. It's a piece of code embedded directly in the smart contract that continuously monitors critical parameters. The moment an anomaly is detected, the circuit cuts off instantly.
Concretely, here's what a circuit breaker can monitor:
Sudden price swings. If a token's price jumps or crashes more than 10% in minutes, that's suspicious. The protocol can then temporarily block withdrawals or borrowing on that asset. This is exactly what happened with Venus: the protocol detected that the XVS price was being artificially manipulated and froze operations until the situation stabilized.
Abnormal volumes. A lending protocol knows its typical activity level. If suddenly someone tries to borrow 50 times the average volume, that's a red flag. The circuit breaker can automatically cap the maximum borrowable amount in a single transaction.
Suspicious transaction chains. Some protocols analyze transaction patterns. If a user borrows, swaps, deposits, and re-borrows within the same second, the system can detect an attempt at abusive arbitrage or manipulation.
The beauty of this system is that it works without human intervention. No need for an analyst monitoring dashboards at 3 a.m. The code detects, the code reacts, the code protects.
Nora's take: the thermostat analogy
Imagine your home boiler. You set the thermostat to 20°C. If the temperature climbs to 25°C because something malfunctions, the thermostat automatically cuts off the heating. You don't need to be there watching. That's exactly what a circuit breaker does: monitor the protocol's "temperature" and cut off if things overheat.
Real-time detection: when oracles become sentries
A circuit breaker can only function if it has reliable information. That's where oracles come in—services that provide smart contracts with real-world data, particularly asset prices.
For a long time, DeFi protocols relied on a single oracle. The problem? If that oracle is compromised or provides faulty data, the entire system can be manipulated. This is called an oracle attack, and it has caused substantial losses.
Today, serious protocols use multiple price sources simultaneously. Chainlink, for example, aggregates data from dozens of exchanges before providing a median price. If one source diverges sharply from the others, it's automatically excluded.
But even that isn't always enough. That's why some protocols have developed multilayered detection systems. Venus, after its 2022 incident, implemented what they call "composite surveillance":
- First layer: price comparison across multiple oracles (Chainlink, Band Protocol, decentralized aggregators)
- Second layer: analysis of actual liquidity on exchanges (is there really enough volume to justify this price?)
- Third layer: detection of abnormal user behavior
If all three layers simultaneously signal an anomaly, the protocol automatically activates protection mode: pause borrowing, limit withdrawals, alert the security team.
Donation attacks: the invisible threat Venus also had to face
Now let's discuss a more subtle threat that Venus also encountered: the donation attack. The idea is devilishly simple.
Imagine a lending protocol. You deposit $100, and the protocol gives you 100 tokens in return representing your share of the pool (let's call them "shares"). If someone else deposits $100 afterward, they also receive 100 shares. So far, so good.
Now imagine an attacker sends $1 million directly to the smart contract, bypassing the normal deposit function. The contract receives this money but issues no shares in return. Result? The value of each existing share skyrockets artificially. Your 100 shares are now worth much more.
Why do this? Because the attacker might have deposited a huge amount just before, received shares, then artificially inflated their value with this donation. They then withdraw their funds with massive profit, at the expense of other users whose shares are now worth less than what they deposited.
The solution implemented by Venus and other protocols is elegant: they modified the share calculation formula to be resistant to donations. Technically, they introduced a mathematical "offset" so that even if someone sends funds directly to the contract, it doesn't affect the ratio between shares and the pool's total value.
This is a perfect example of how security in DeFi evolves: each attack reveals a vulnerability, and the community develops a solution that eventually becomes a standard adopted across all protocols.
What you need to know
Circuit breakers are DeFi's fuses. They automatically monitor anomalies (prices, volumes, behavior) and shut down dangerous operations before it's too late—as Venus proved by stopping a $200 million attack.
Detection relies on reliable and multiple data sources. Modern protocols no longer trust a single price source. They cross-check multiple oracles, analyze actual liquidity, and detect suspicious patterns to prevent manipulation.
Each attack strengthens the ecosystem. Donation attacks, abusive flash loans, and other exploits force developers to continuously improve protection mechanisms, which then become standards adopted industry-wide.
The fragile balance between security and decentralization
There is, however, a fundamental tension that DeFi protocols must manage. The more automated protection mechanisms you add, the more complexity you introduce into the code. And in software, complexity often rhymes with new vulnerabilities.
Worse still: some circuit breakers can be hijacked. If an attacker understands precisely at what threshold the protocol cuts operations, they can manipulate the system just below that threshold, or deliberately trigger the circuit breaker to lock out legitimate users.
That's why the best protocols don't just code protections. They have them audited by multiple independent security firms, run "bug bounties" where ethical hackers search for vulnerabilities for rewards, and maintain complete transparency around their code.
Venus, after its incident, published a detailed post-mortem of the attack, explaining exactly what happened and how they strengthened their defenses. This transparency is also a form of collective protection: when a protocol shares lessons from an attack, all other protocols benefit.
DeFi remains high-risk territory. But unlike the early days when protocols were easy targets, the ecosystem has matured. Circuit breakers, real-time monitoring, and protections against sophisticated attacks like donation attacks don't guarantee absolute security. Nothing can. But they transform DeFi into an environment where stealing funds becomes a little harder every day, a little more detectable, and a lot less profitable for attackers.
This evolution in smart contract security is all the more crucial as more and more investors use DeFi protocols to generate yields on their digital assets.
And perhaps that's the best defense you can hope for in a world without central authority: making an attack so complex and risky that it simply isn't worth the effort anymore.



