In December 2024, Google published a technical report that sent shockwaves through the Bitcoin ecosystem. The company demonstrates that a sufficiently powerful quantum computer could compromise Taproot addresses — Bitcoin's most recent major innovation, adopted in 2021 — well before other address types. This revelation about the quantum computing risk to Bitcoin Taproot is far from trivial if you hold bitcoins on addresses beginning with "bc1p".
Imagine you've installed a next-generation lock on your door. It's more convenient, more discreet, and everyone tells you it represents the future. Except that this lock, because of its very design, would be the first to give way to a new kind of master key. That's exactly the situation Google reveals with Taproot and the threat of Taproot quantum attack.
Before succumbing to panic, let's take time to understand what's really at stake. The quantum threat isn't imminent, but it's no longer science fiction either. And most importantly, there are concrete measures you can take right now to ensure Bitcoin security for the long term.
Why Taproot is more vulnerable than other Bitcoin addresses
To grasp the problem, you first need to understand how Bitcoin protects your funds. Each Bitcoin address relies on a key system: a private key (known only to you) and a public key (visible on the blockchain). Your private key allows you to sign transactions, proving you're the rightful owner of the bitcoins.
Traditional Bitcoin addresses — those beginning with "1" or "3" — use a dual protection mechanism. Your public key only appears on the blockchain when you spend your bitcoins. Before that, only a "hash" (a cryptographic fingerprint) of this key is visible. It's as if your lock remains hidden behind a panel until the moment you use it.
Taproot, by contrast, directly exposes the public key as soon as the address is created. This transparency isn't a design flaw: it enables advanced features like Schnorr signatures, which make multi-signature transactions indistinguishable from simple transactions. In terms of privacy and efficiency, it's a significant step forward.
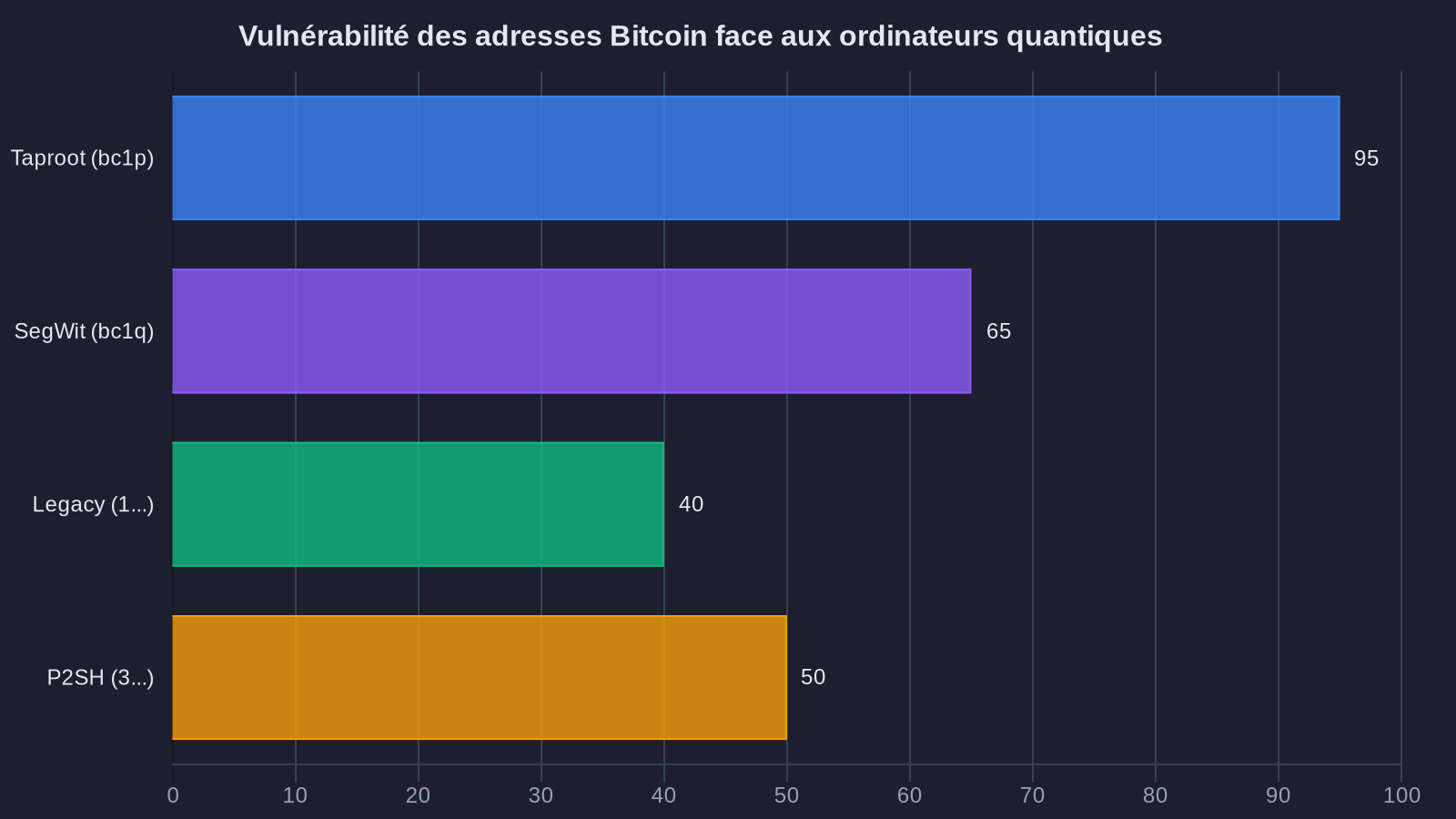
But faced with quantum computers, this exposure changes everything. Google demonstrates this in its report: with a quantum computer equipped with several million qubits (quantum computing units), an attacker could derive your private key from your public key in just hours. For Taproot addresses, this public key is already visible. For traditional addresses, the attacker would first need to "crack" the hash, adding a considerable layer of complexity.
Nora's take: the safe deposit box analogy
Imagine two safes in a bank. The first (traditional address) sits in a locked room, and you only see the safe's lock when you enter the room. The second (Taproot address) is right in the lobby, lock visible. With today's tools, both safes are impenetrable. But if tomorrow a tool appears that can copy any lock just by photographing it, guess which one will be cracked first?
Where the quantum threat to Bitcoin cryptography really stands
Let's be frank: nobody currently owns a quantum computer capable of threatening Bitcoin. The most advanced machines today, including Google's recently announced Willow processor, have around 105 qubits. To attack Bitcoin, you'd need several million. And not just any qubits: stable qubits with an extremely low error rate.
Researchers estimate it will take 10 to 20 years before such a computer exists. Some say 30 years. Others, more optimistic (or pessimistic, depending on your perspective), mention 5 to 7 years if progress accelerates. In short, we don't know exactly when, but we know it's coming.
What makes Google's report important is that it quantifies the threat precisely. According to their calculations, a quantum computer with 13 million qubits could crack a Taproot address in approximately 8 hours. For a traditional P2PKH address (those starting with "1"), it would take more than 2,600 years with the same machine. The difference is staggering.
Another key element: the attack window. To steal your bitcoins, an attacker would need to compute your private key before your transaction is confirmed on the blockchain. In practice, this gives them roughly 10 minutes (the average time between Bitcoin blocks). With a sufficiently fast quantum computer, it's doable for Taproot. For traditional addresses, even with an ultra-powerful quantum computer, the window is too narrow.
What you should do if you hold bitcoins on Taproot
You have bitcoins on an address beginning with "bc1p"? No need to panic immediately, but measured vigilance is warranted. Here are the concrete recommendations emerging from expert analysis on cryptographic key migration.
First step: identify your addresses. Open your wallet and check what types of addresses you're using. Taproot addresses begin with "bc1p". SegWit addresses (older but still quantum-safe) begin with "bc1q" or "3". Legacy addresses begin with "1".
Second step: migrate gradually. If you hold a significant portion of your bitcoins on Taproot, consider transferring them to P2PKH ("1") or P2SH ("3") addresses. These formats, though technically older, offer better protection against the quantum threat. Yes, transaction fees will be slightly higher than with Taproot, but security is worth that investment.
Caution: this migration isn't urgent in the "within 48 hours" sense. But it shouldn't be put off indefinitely either. A reasonable approach would be to make these transfers over the coming months, taking advantage of periods when Bitcoin network fees are low.
Third step: diversify your security strategy. If you use a hardware wallet (Ledger, Trezor, etc.), verify that your firmware is up to date. Manufacturers closely monitor quantum threat developments and will propose solutions when necessary. Some researchers are already working on "quantum-resistant" signature algorithms that could be integrated into Bitcoin via a future protocol upgrade. This post-quantum cryptography approach represents the future of blockchain security.
The special case of dormant bitcoins
One situation deserves particular attention: bitcoins that have never been moved from their original address. If you mined or bought bitcoins several years ago and they've never moved, check the address type. Very old addresses (predating 2017) are generally in P2PKH format, so relatively protected. But if you adopted Taproot starting in 2021-2022 to take advantage of its benefits, your funds are potentially in the medium-term risk zone. Cryptoasset security requires vigilance comparable to that needed to protect your funds in DeFi.
Will Bitcoin adapt? Probably, but not without debate
The Bitcoin community hasn't sat idle facing the quantum threat. Several technical proposals are already circulating to make the network "quantum-resistant". The general idea is to integrate new signature algorithms, based on different mathematics, that resist quantum attacks.
The problem is that any modification to the Bitcoin protocol requires very broad consensus across the community. Bitcoin doesn't have a CEO who decides overnight. Every major change undergoes technical, economic, and philosophical debates that can last years. Taproot itself took nearly four years between initial proposal and actual activation.
Some developers advocate for preventive action right now: integrating quantum-resistant algorithms before the threat becomes imminent. Others believe we should wait until we have more certainty about quantum technologies themselves. A third camp argues that Bitcoin will adapt naturally when the time comes, without need for haste.
What's certain is that when the threat becomes tangible (probably when the first quantum computers with hundreds of thousands of qubits emerge), pressure to act will be immense. The financial stakes — we're talking about hundreds of billions of dollars — guarantee that the community will find a solution. This adaptive capacity echoes how DeFi protocols have developed protection mechanisms against emerging threats.
What to remember about the quantum risk to Bitcoin
First point: Bitcoin Taproot addresses ("bc1p") are more vulnerable to future quantum attacks than previous address formats, due to the direct exposure of the public key. Google's report quantifies this vulnerability with precision.
Second point: the threat isn't imminent (likely 10 to 20 years away), but it's no longer theoretical. Progress in quantum computing is accelerating, and prudence dictates anticipating rather than reacting in crisis mode.
Third point: you can take action right now by gradually migrating your bitcoins to P2PKH or P2SH addresses, which offer better resilience to quantum threats. This approach doesn't demand haste, but shouldn't be postponed indefinitely either.
Google's revelation reminds us of a fundamental truth: security in the digital world is never permanent. It evolves with technology, and what was unbreakable yesterday can become vulnerable tomorrow. Bitcoin has already overcome many technical challenges since its creation in 2009. The quantum threat will be another, probably the most complex to date. But unlike other threats, this one has the advantage of being foreseeable. We have time to prepare. As long as we don't wait until the last moment.



